Reporting Config
This tab helps to configure the policies and settings to designate the targets that DSI data will be directed to. To access this tab, go to Reporting > Config in PEM (PK Endpoint Manager).
Data Security Intelligence
This panel lists down the DSI policies that are currently in use. You can edit or delete any DSI policies.
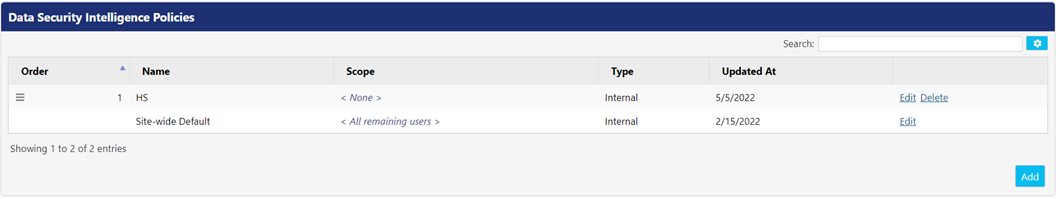
- Edit - Click this button to edit the details of a policy. Steps of editing a policy are same as adding a DSI policy. While editing the Site-wide Default policy, only Agent Options and Target Type can be configured.
- Delete - Click this button to delete a policy. You cannot delete the Site-Wide Default policy.
Adding a DSI Policy
Click Add button to add a DSI policy in the PEM. The Add Data Security Intelligence Policy screen appears.
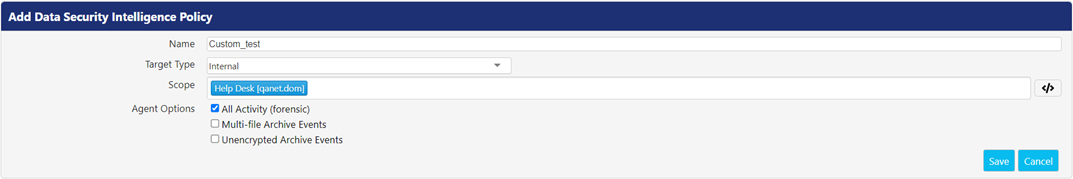
Following is the description of the fields which appear while adding or editing a DSI policy.
| Fields | Description |
|---|---|
| Name | Enter the unique name of the DSI policy. |
| Target Type | This drop-down provides the list of all available targets for DSI events.
|
| URL | Enter the URL of the server chosen in Target Type drop-down. This field does not appear when Internal is opted as target type. |
| Index | Enter the index name to be used for Elastic Search. This field is visible when Elastic Search is chosen as target type. |
| Token | Enter the token provided from Splunk server. This field is visible when Splunk is chosen as target type. |
| Scope | Select the Active Directory users or groups that are assigned to a particular DSI policy. You can use Advanced Definitions by clicking |
| Agent Options | The Agent Options checkboxes allow the administrator to specify which types of events are subject to the policy.
|
Data Security Intelligence Global Settings
This panel provides a set of global properties that are applied wherever the DSI policy is targeted. Click Edit button to edit the listed properties.

Following is the description of properties:
| Settings | Description |
|---|---|
| Enabled | Select this option to enable DSI to be generated. |
| Signing | Select this option to generate DSI events related to digital signing activities. |
| PK Endpoint Manager | Select DSI policy that you want to apply to the PEM generated events. |
| Log Device Last Access Times | Select this option to have DSI log the time when last access was made into the device in the events. |
| Log Admin Login Attempts | Select this option to include Admin Login Attempts to the events that are DSI generates. |
.png)
